Getting started with INKY
Written By Eric Heller
Last updated 16 days ago
What is INKY?
INKY is Kaseya’s best-in-class email security solution, designed to protect your organization from phishing and email threats.
INKY uses multiple AI detection methods (computer vision, GenAI, behavioral analysis, link analysis, sender authentication) to catch sophisticated email threats. Transparent warning banners explain threats in plain language, building user trust and awareness.
For more information, see the article Understanding INKY Basics.
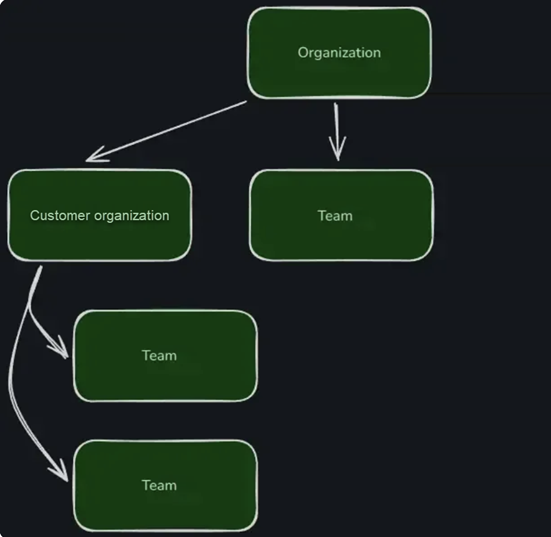
Organizations and teams
Organizations are INKY's highest-level entity for grouping teams and managing hierarchy. Organizations provide a structure for organizing multiple teams, assigning administrators, and controlling settings across the entire account.
In INKY, teams typically represent small to medium-sized businesses (SMBs). Teams can be nested within organizations to maintain hierarchy and streamline management. An organization can have multiple teams, each with its own set of administrators and settings.
An organization automatically includes the following entities:
Root organization: INKY's highest-level entity, the MSP. The root organization can include many customer organizations. Root organizations are represented with a building icon.

Root organization’s team - This is the MSP’s/MME’s own team for which they can deploy and become familiar with INKY. Teams are represented with a people icon.

Customer organization - These sub-organizations are the customers of the root organization. Customer organizations can have many teams and are represented with a people icon.

Onboarding
IMPORTANT: Only users with the Super Admin account can perform Onboarding tasks.
This Onboarding section guides you through the essential tasks required to ensure a successful onboarding experience. It is recommended you perform the tasks in each section in the order they are presented.
IMPORTANT: A section may refer you to a separate article with instructions for completing the task. After you complete the task, be sure to return to this “Getting started with INKY” article and move to the next section to continue onboarding.
1. Installing INKY for your organization’s own team
Installing INKY for your organization’s own team is a great way to become familiar with INKY’s features and deployment strategies.
For more information, see the article Installing INKY for your own organization’s team.
2. Installing INKY for a customer organization
Generating a license and installing INKY in the client's email platform are key steps when installing INKY for a customer organization.
For more information, see the article Installing INKY for a customer organization.
3. Configuring essential features
After installing INKY for your own organization or a team, you should configure several essential features to ensure optimal protection and accurate threat detection.
Understanding inheritance
To configure features effectively, it is important to understand how inheritance works in INKY. Features and policies configured at the root organization level are automatically inherited by all of the organization’s child teams. When a feature is configured at the team level, that setting overrides the inherited configuration for that specific team.
For more information about inheritance, see the article Organization Settings and Inheritance.
Admin Center
Essential features are configured from the Admin Center.

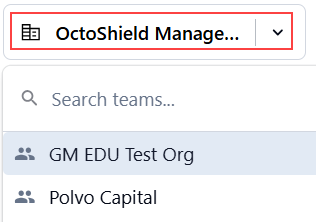
From the Team Selector drop-down, select the team for which you want to configure features. It is recommended that you configure feature settings at the partner level (building icon) first and then adjust them as needed at the team level (people icon).
Analysis Settings
The Analysis Settings page contains key features that control how INKY analyzes and detects threats in your email environment. To access this page, click Analysis in the left navigation menu.
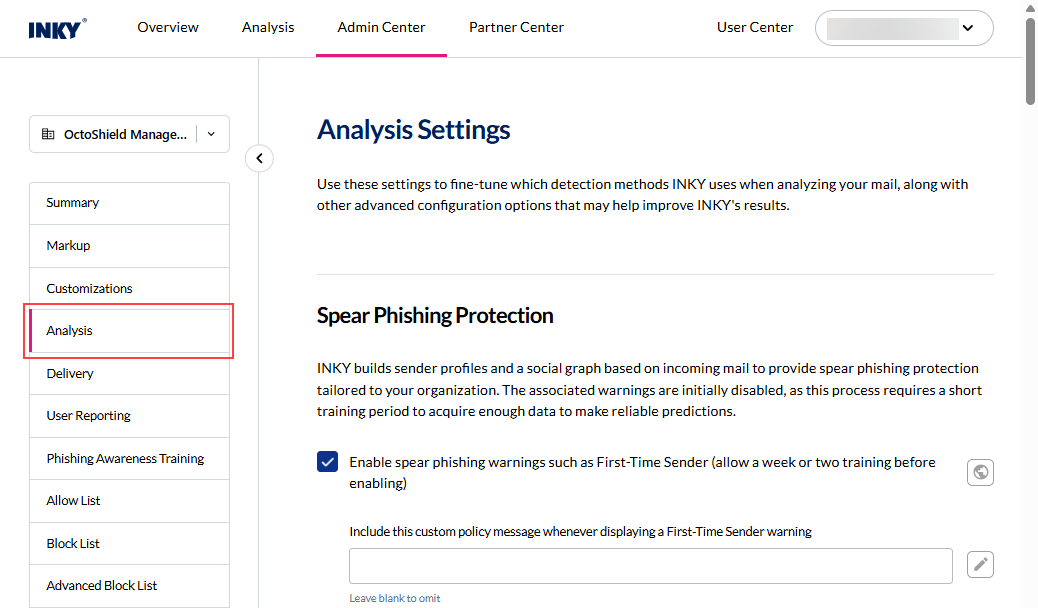
Note: Features that support enable/disable functionality are listed with their default status.
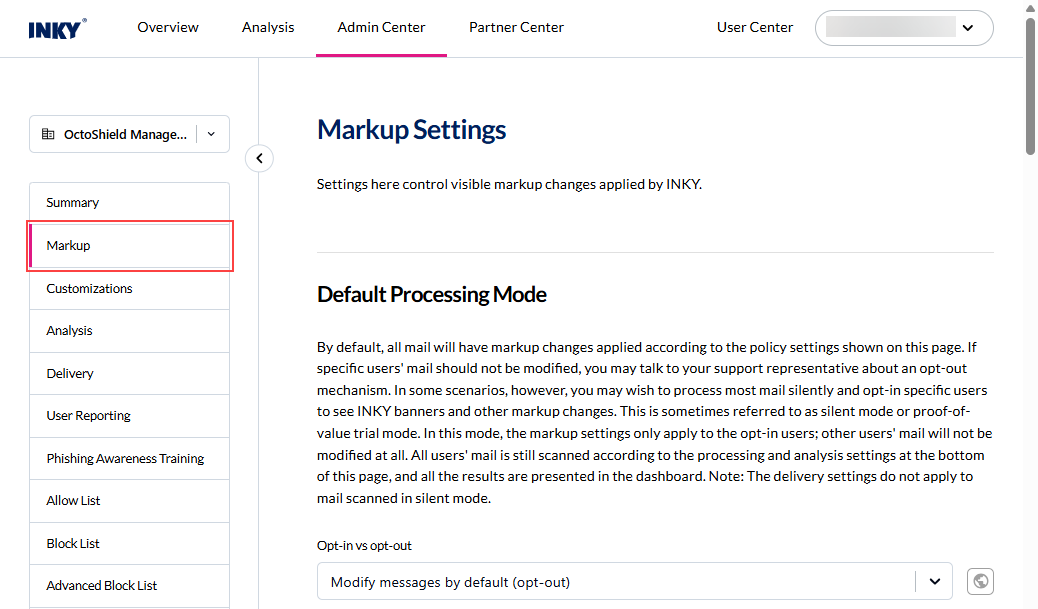
Markup Settings
The Markup Settings page includes key features that control the visible markup changes applied by INKY to email messages. To access this page, click Markup in the left navigation menu.
4. Understanding group management
Organizations can assign users to one of three INKY user groups. While all three groups may be used, each user can belong to only one group. The assigned group determines how INKY analyzes and processes email for those users.
Include Group: Users in the Include Group are fully protected by INKY email security.
Exclude Group: Users in the Exclude Group are not processed by INKY. INKY does not provide email security for these users.
Journal Group: Users in the Journal Group are protected by INKY email security. However, INKY does not provide user‑facing visibility. Warning banners are not added to emails and emails are not blocked or quarantined.
When users are assigned to the Journal Group, INKY operates in Journal mode for those users. In Journal mode, INKY receives and analyzes all email. The Dashboard displays what would have been detected, allowing administrators to review threats INKY identifies in the environment and build allow lists for legitimate senders.
Recommended group management approach
It is highly recommended that you begin managing your users by adding a small number of them to the Journal Group only.
IMPORTANT: At this stage of onboarding, do not add any users to the Include Group.
For more information about user groups and how to assign users to a group, see the article Group management.
5. Planning your deployment strategy
INKY uses a two-phase deployment approach that minimizes user disruption and false positives:
Phase 1: Journal Mode (3-7 days): During Journal Mode, INKY provides passive email monitoring with no user visibility. INKY's social graphing begins building your organization's email network map. This reduces first-time sender alerts later.
During Journal mode, you monitor how INKY processes email for users in the Journal Group and adjust policies as needed.
Note: For detailed steps on monitoring emails while INKY is operating in Journal mode, including examples of how to review and act on specific emails, see Monitoring email while in Journal Mode.Phase 2: INKY-Users Group: After completing Journal Mode, you can add users to the Include Group to receive full inline INKY protection with banners. To ensure a smooth rollout and minimize user impact, it is recommended to add users gradually in batches.
For more information, see the article Deployment strategy.
6. Adding account users
Super Admins can add users who have access to and work within their INKY environment. There are multiple roles available, each with specific permissions. When adding a user, make sure to select the appropriate role based on the level of access required.
For more information, see the article Admin management.
Frequently asked questions
For answers to common INKY questions, see the article General Q&A.