Account Takeover (ATO) Detection
Written By Matt Sywulak
Last updated 1 day ago
Account Takeover (ATO) Detection is a beta outbound security feature that monitors your users' sending behavior for signs of a compromised email account. When suspicious activity crosses a configured threshold, INKY automatically places the affected user into enforcement mode — quarantining, discarding, or delivering their outbound messages according to your policy while alerting designated approvers to review and act.
ATO Detection requires INKY Pro and is gated as a beta feature. Contact your account team to have it enabled for your organization.
How it works
INKY continuously scores outbound messages from each sender using three signal types. When a user's cumulative score crosses a threshold, they enter enforcement mode at the corresponding risk level.
Signal types
Risk levels
Signal scores accumulate into one of three risk levels. The score thresholds are fixed — you configure what action INKY takes at each level, not the thresholds themselves.
Enforcement mode
When a user's score crosses a configured threshold, they enter enforcement mode. While in enforcement:
All outbound messages are handled according to the Enforcement Action you configured for their risk level (Deliver, Quarantine, or Discard).
Enforcement stays active for the Time in Force you set (1 hour to 7 days). If new signals above threshold arrive during enforcement, the window resets and extends.
Quarantined messages that an administrator has not manually approved are automatically rejected when enforcement expires.
All administrators listed as ATO Enforcement approvers in Global Workflow Approvers are notified immediately and can review messages and release the user at any time via the Triage page.
Configuration
ATO settings are in Settings → Outbound Protection → Account Takeover Settings.
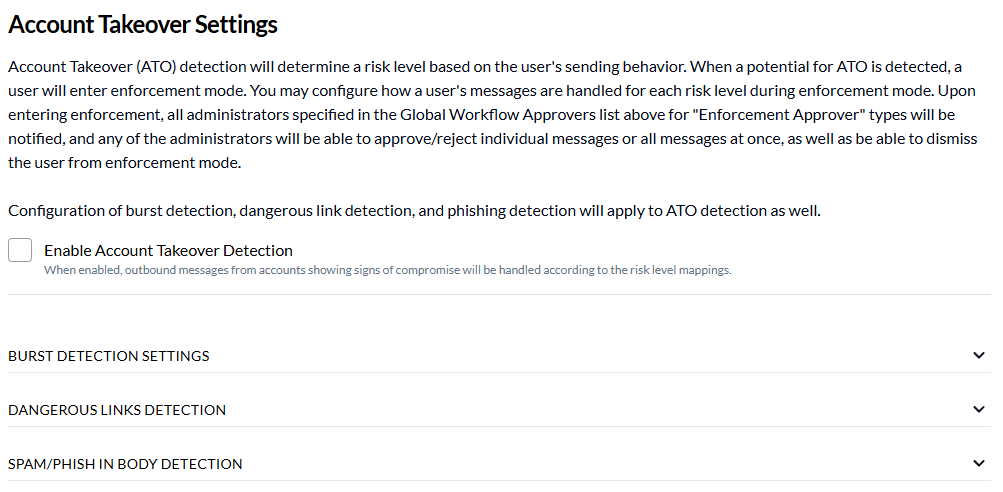
Step 1: Enable ATO detection
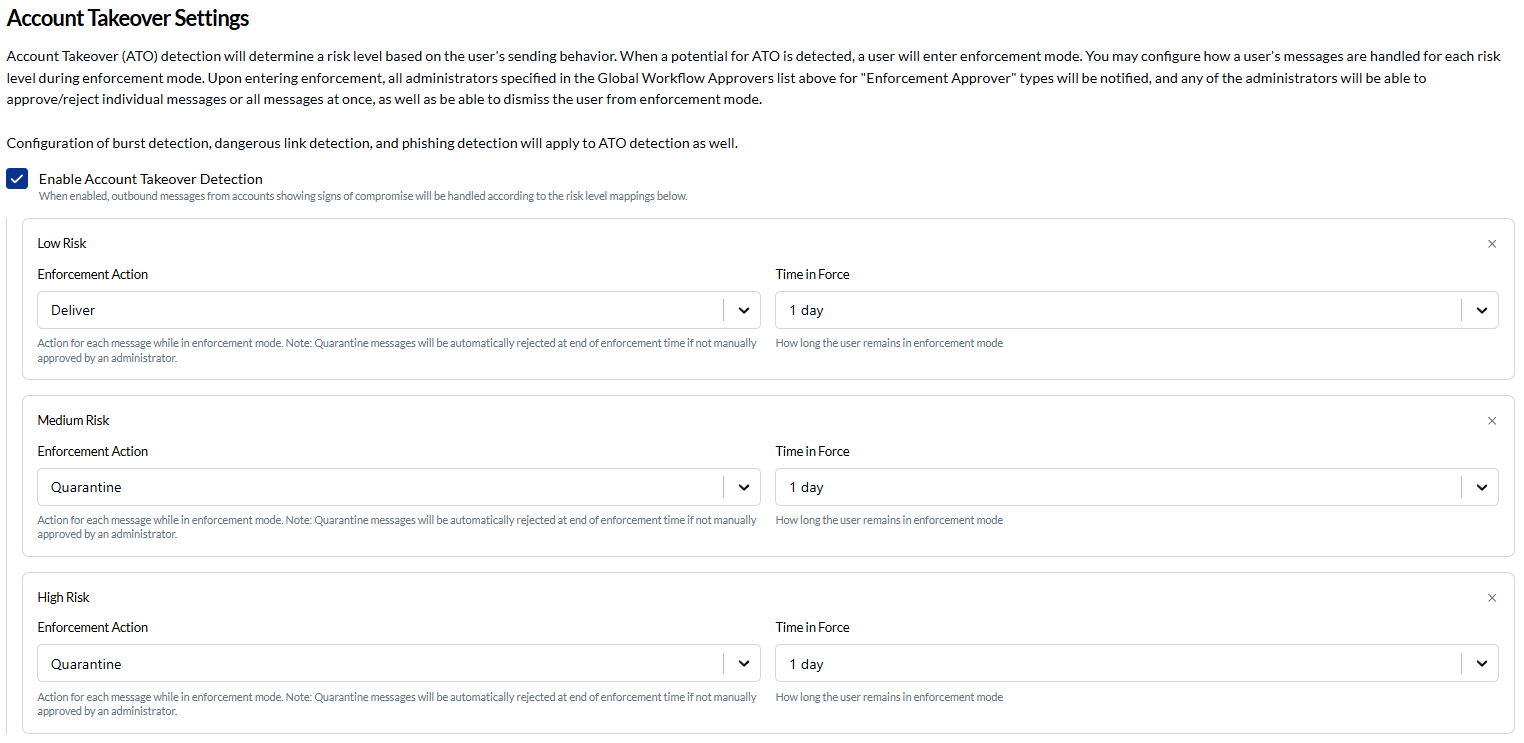
Check Enable Account Takeover Detection. When disabled, outbound messages are unaffected regardless of any risk map entries you have configured.
Step 2: Configure risk level actions
Click + Add Low Risk Action, + Add Medium Risk Action, or + Add High Risk Action for each risk level you want to enforce. You can configure Low, Medium, and High independently — any level you don't configure defaults to normal delivery.
For each level, set two options:
Step 3: Add ATO Enforcement approvers
Administrators who should be notified and able to act on enforcements must be added to Global Workflow Approvers with the type ATO Enforcement.
In Outbound Protection settings, scroll to Global Workflow Approvers.
Click Add Approver, select the administrator, and choose ATO Enforcement as the approver type.
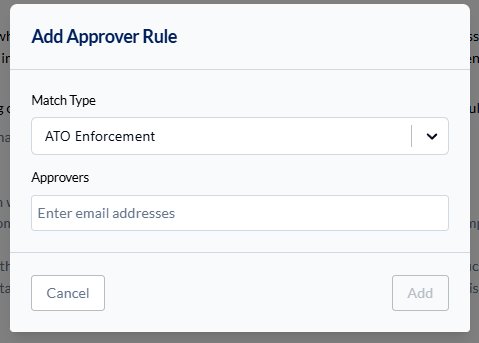
All ATO Enforcement approvers are notified by email when a user enters enforcement and can take action from the Triage page.
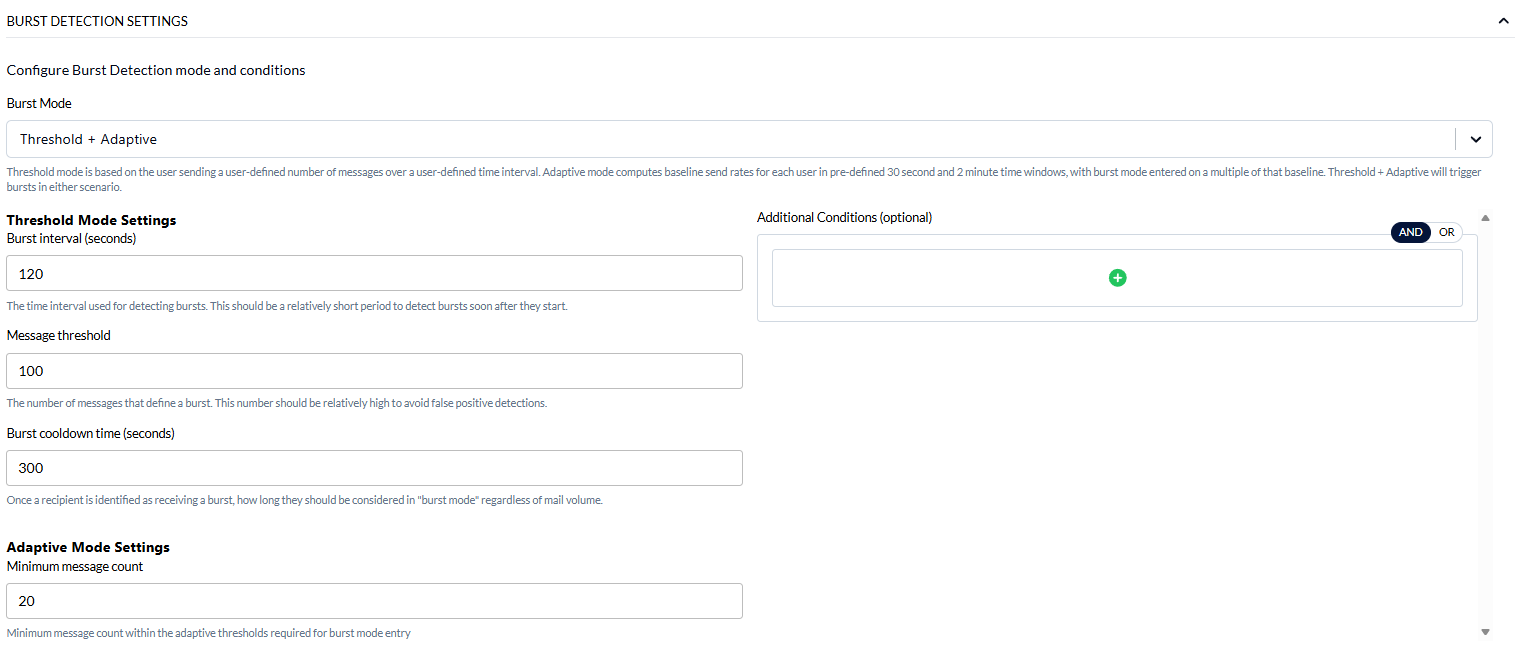
Signal sensitivity
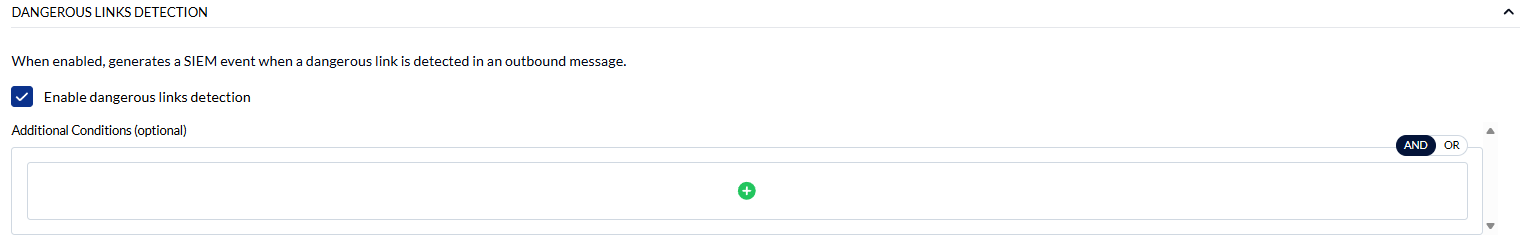
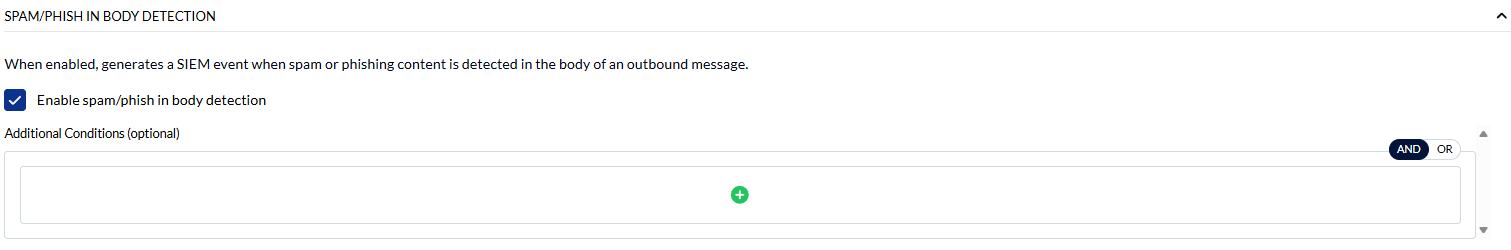
ATO detection uses your existing outbound signal configurations as inputs — it does not have separate sensitivity settings. To tune what triggers ATO, adjust your Burst Detection, Dangerous Link Detection, and Spam/Phishing Detection settings in Outbound Protection.
Enable Dangerous Links Detection
Enable Spam/Phish Body Detection
Permissions
Frequently asked questions
What happens if I haven't configured an action for a detected risk level?Messages are delivered normally. Only risk levels with an entry in the risk map trigger enforcement.
Can enforcement be extended automatically?Yes. If new signals above threshold arrive while a user is already in enforcement, the Time in Force window resets from that point, extending the enforcement period.
What happens to quarantined messages when enforcement expires?Any messages still in quarantine that were not manually approved are automatically rejected (discarded).
Does ATO affect inbound email?No. ATO detection is outbound only.
Does ATO use my existing burst and link detection settings?Yes. Your configured Burst Detection, Dangerous Link Detection, and Spam/Phishing Detection settings all feed into ATO scoring.